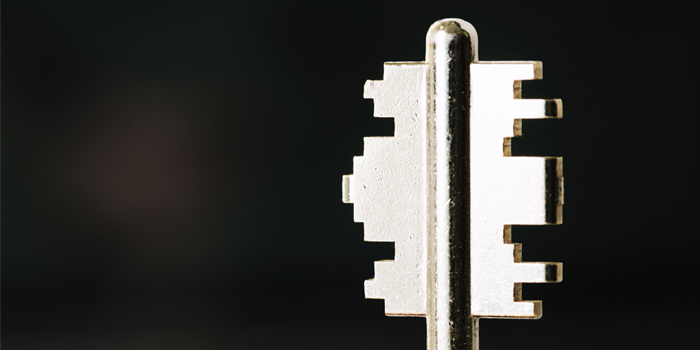
A – Z of Cybersecurity
Whether you are an IT expert, use the computer at work or at home or just use the internet for fun, this article is for you. Cybersecurity is no longer the responsibility of the security engineers, rather everyone is responsible for enhancing cybersecurity. This article provides explanation to common cybersecurity terms that you should be … Read more